What makes Zoom a Secure Video Platform
by VIDIZMO Team on February 09,2022

The COVID-19 pandemic has brought a major shift in the business landscape & how we used to communicate.
Businesses are shifting towards remote work & hybrid models. It might seem like a lifetime, but these video conferencing solutions like Zoom, Microsoft Teams, etc., weren’t as well-known as they’re now. It looks like everyone has now adopted one of these platforms for educational & official purposes.
The most famous video conferencing solution we’ll have heard & use is Zoom. It has become so universal that even kids use “Zoom me” as a verb to communicate. The company has announced 300 million daily meeting participants in April 2020.
People have been using Zoom live streaming for most of their virtual communication, from online classes to sensitive discussions. But with each new technology comes new security risks that organizations must combat.
-
Is Zoom safe to use for work meetings?
-
Can Zoom record your work meetings?
-
How do you securely manage your recorded work meeting
Let’s look at some of the Zoom security concerns & Zoom security best practices to have a smooth and secure experience.

Is Zoom Safe to Use?
So, is Zoom safe or not? And what are some of the Zoom security vulnerabilities that people or organizations are concerned about?
To cut it short, yes, Zoom is secure for most organizations that have reasonable security measures in place.
Let’s have a detailed look into this.
Before going for any video conferencing solution like Zoom, there are a few questions you need to ask:
-
What sector/industry are you working in?
-
Are you going to discuss extremely sensitive data that could impact the country’s security?
-
Will your Zoom meetings involve trading/sharing or creating an intellectual property or state secrets?
-
What’s your government’s say on a service provider like Zoom?
To take the risk-based approach to solve the mystery “how secure is Zoom?” you need to respond to the above questions, & then you’ll have your answer.
Misconceptions & Myths About Zoom
Before discussing Zoom security best practices, let’s bust some myths first.
Many people think Zoom is a Chinese company. Well, to clear your misconception, Zoom is a US-based company headquartered in San Jose. The CEO himself clarified that they have no connections with the Chinese government.
Here are a few other myths clarified by Zoom’s CTO, Brendan Ittelson, in his blog. Let’s have a brief look:
-
Many organizations have this concern about Zoom security vulnerabilities that “only paid Zoom meetings are encrypted.” Fact checks: All free & paid Zoom meetings between clients are protected with 256-bit AES-GCM encryption in transit. You can also enable the optional end-to-end encryption feature for your meetings. Or use an encrypted zoom meeting passcode.
-
There’s a myth believed by many that even if you’re on mute, the meeting hosts can hear you. Well, that’s not true! As cleared by the CTO, Zoom doesn’t offer the ability to unmute or listen to the meeting participants secretly.
-
Another myth busted by the CTO is, pinning a video doesn’t notify anyone in the meeting. It’s for your device only.
-
Zoom doesn’t track your activities, usage, or productivity. It can’t track if you’re using any other app during a Zoom meeting.
-
And here’s the last one, Zoom works perfectly fine with Chromebooks, with the same functionality as Mac & Windows.
12 Must-Follow Zoom Security Best Practices
-
Allow Authenticated Participants Only
One of Zoom security best practices is allowing authenticated IDs to log in and attend the meetings. It will ensure that outsiders cannot enter the meeting uninvited even if they access the meeting URL. It will be even more secure to enable two-factor authentication to verify each user and ensure that a cyber breach does not occur.
-
Don’t Share the Meeting URL Openly
It is equally important not to share the meeting link openly on a social media platform. Just share the link with each participant or a private group. The participants should also be advised not to share this link further with any other person.
-
Meeting Host Must Retain Control
The meeting host should fully control all the Zoom security settings to restrict meeting access, limit participants’ feature usage and enable important privacy features. Set a strong password for meeting attendees’ entry.
-
Keep “Host-Only” Settings
Automatically mute and close the video of the participants entering the meeting and immediately remove any suspicious participants. Keep all the settings to “Host-only” with team members manually given access to any particular feature they need to utilize for discussion.
-
Maintain Zoom Meeting Recordings
Recording all the Zoom meetings with participants’ consent is crucial for future viewing, accountability, training, and accessibility to the participants who could not attend it due to some other engagement. Make your work meetings valuable assets that can be used in the future without losing out on security.
But, how is this possible?
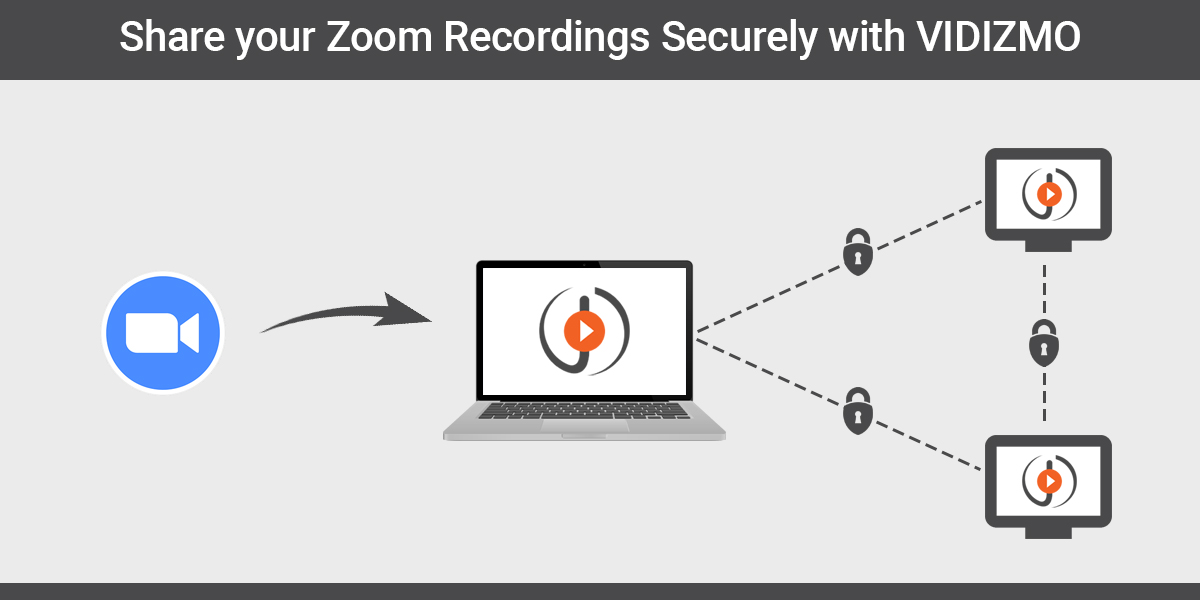
An organized video library for smart search and scalable storage is required to securely make your Zoom meeting recordings accessible. This is where video conferencing solutions fall short, potentially leading to a leak of confidential business information.
Follow this Zoom security best practice rather than individually emailing or messaging the link to the recorded meeting:
Opt for a powerful enterprise video platform like VIDIZMO EnterpriseTube that can automatically ingest recorded online meetings from platforms like Zoom and MS Teams. These recordings will be seamlessly published and readily playable on VIDIZMO’s secure YouTube-like secure video platform.
You can also benefit from many other critical video content management capabilities that Zoom cannot provide, like restricting recording access to certain users or groups.
Learn More: How to securely share a recorded zoom meeting?
Or read this detailed guide for further information:
-
Be Cautious of Sharing
Another critical Zoom security setting that you should follow is for meeting hosts to restrict participants’ files and screen sharing ability as a default setting. Then, manually giving the rights to an authenticated attendee who needs to share a file or screen.
Previously, online meeting bombing incidents have led to attendee privacy and data leakage breaches. Such incidents can potentially taint a company’s reputation or put them at a competitive disadvantage.
-
Maintain an Audit Log
An audit log must be maintained for all the activities performed on the meeting recordings. These audit logs help track any suspicious activity and help meet critical compliances for personal data protection like GDPR for EU residents and HIPAA for the healthcare industry.
But, how is this possible?
As mentioned above, Zoom & other video conferencing solutions cannot track the activity performed on recordings once they are shared. This is a problem as these recordings contain personal data that could cause a security breach.
Hence, a major Zoom security best practice is to opt for an enterprise video platform like VIDIZMO to securely store and share your recordings where these audit logs are continuously maintained.

VIDIZMO meets all major compliance requirements like GDPR and HIPAA. It maintains not only a platform-wide audit log but also an audit log for each participant.
These records can be exported as PDF or CSV files and include activities like who was assigned access to a recording, what time they viewed it, their IP address, whom they share it further with, etc
-
Browser-based Video Conferencing
Another vital security best practice is opting for a video conferencing solution with a browser-based web application like Zoom. This is important for meeting attendees that do not have virus protection and up-to-date security settings on their devices. It also ensures that they gain access to an up-to-date solution.
-
Regularly Update the Application
It is critical to encourage all your employees to follow this Zoom security best practice. Every meeting attendee should ensure that their software is updated with the most recent security updates to the latest version. It’s recommended to have the automatic updates setting enabled on all the employees’ devices.
-
Enable Waiting Rooms & Lock Meetings
Meeting hosts should have the attendee waiting rooms option enabled for the meetings they create. With this option enabled, attendees will first enter a waiting room upon clicking the meeting URL. The meeting host can then verify their ID and approve them entering the meeting.
Once all important participants have entered the meeting, the meeting host must lock it immediately so that no unauthorized person gains entry. Any suspicious participants can be removed from the waiting room by the host.
-
Opt for End-to-End Encryption
Always opt for a video conferencing solution with end-to-end encryption available to maintain complete privacy of all your video calls, even from the solution provider. Without such protection, malicious hackers might be able to find security holes to breach and leak your data.
-
Keep Chat Usage to Minimal
Lastly, disable video chat unless absolutely needed. It is especially hard to monitor in larger meetings. Some attackers use these chats to send unsafe phishing links that could lead to a security breach in the participants’ devices that click those. If the chat has to be enabled, request meeting participants not to misuse it and be careful of any suspicious links.
How to Use Zoom & VIDIZMO Together to Work in a More Secure Environment?
There is no denying the benefits of video conferencing. Rather than holding back from these revolutionary tools due to security concerns, embrace them quickly with the right security practices implemented.
Zoom is one of the most used video conferencing tools. As mentioned in the blog earlier, one of the Zoom security best practices is to record your Zoom meetings for later use. Many organizations are following this practice. But there are a few limitations regarding video sharing & management offered by Zoom.
The ultimate solution is to use Zoom with an enterprise video management platform, like VIDIZMO. It’s a YouTube-like video platform for business use cases. Once integrated, it will automatically ingest recorded online meetings from platforms like Zoom and MS Teams.
Here are just some of the capabilities your organization can benefit from:
- Bulk sharing with different organizational teams in a secure video hosting platform with end-to-end encryption
- Access can also be restricted based on employee roles that can be pre-set on VIDIZMO
- Organize content into various playlists and collections and share these with teams to be used in scenarios like employee training courses
- Add in-video interactive elements like quizzes and handouts in your training recordings
- Multiple expirable recording links can also be shared with external or anonymous users with password protection, limited views and availability duration
- Automatic transcription and its translation in 50+ languages
- Platform-wide and in-video smart search based on indexed automatic tags and keywords generated through spoken words, on-screen text, faces, and objects.
Contact our team today to learn more about how VIDIZMO works with Zoom.
Jump to
You May Also Like
These Related Stories

How to Have Secure GDPR Compliant Online Meeting Recordings?
Share Zoom Recordings Securely with VIDIZMO Enterprise Video Platform


No Comments Yet
Let us know what you think