Evidence Management Practices For Protecting Digital Evidence
by VIDIZMO Team on March 28,2021

In this modern age of technology, digital evidence is an integral part of an entire investigation process. Digital evidence is growing at an exponential rate.
According to Interpol’s review, the digital forensics market is expected to grow by USD 9.68 billion by 2022, a compound growth rate of 15.9% per year.
No doubt, digital evidence is a crucial player in solving criminal cases, but it is more fragile and can easily be tampered with or altered. Court requires sound digital evidence without any alteration. Therefore, protecting digital evidence at every phase is of major concern from its collection to prosecution and court presentation.
When was the evidence collected and why? Who recorded it? Who has accessed it since and what actions are performed on it? How can you prove that the integrity of digital evidence is preserved?
Are there any best ways to secure and protect digital evidence?
If you are wondering about best practices for preserving and securing digital evidence, then you are at the right place.
5 Best Ways to Secure and Protect Digital Evidence:
To make digital evidence legally admissible, you need to bring best practices into play. The following specific ways assist you in preserving and protecting digital evidence in every possible way.
Maintain Orginal File Using Drive Imaging:
Before initiating the process of digital evidence analysis, officers or investigators should image it first. It means to create a bit-for-bit duplicate of an evidence file. In this way, you can retain the original digital evidence file.
Do not perform analysis on the original evidence file (perform any such analysis on its duplicate file). Make sure to limit every action performed on the original digital evidence file, otherwise, the court will not accept it for legal proceedings.
Chain of Custody:
In the judiciary, it is essential to prove the integrity of evidence. You should appropriately handle it by maintaining audit logs detailing: who has accessed it? Who modified it and how? Otherwise, it will not be admissible in court and will not stand against any legal interrogation.
Therefore, protecting digital evidence is a great challenge. You cannot rely on your operating system, e.g., windows itself, to provide you with such a detailed report.
Chain of custody will help you in proving the authenticity of evidence as it provides a complete record of who accessed the file, at what time, and the sequence of activities performed on the evidence by any authenticated user.
Tamper detection:
The process of imaging generates cryptographic hash values. These cryptographic hash values verify the integrity and authenticity of digital evidence by providing proof that any digital evidence is the same as the original since upload.
If any alteration is made to the evidence, the system generates a new hash value that does not match the original one. Hence, through hash values, you can detect any sort of alteration and the integrity of digital evidence is preserved.
Protecting Storage Devices:
The revolutionized world can store gigabytes of information on a device no bigger than a fingernail. If your digital evidence is stored on the laptop or any other device, then protect your device first.
Set a login password that is hard to guess, so that nobody can access your sensitive data such as digital evidence. Use a password-protected screen saver to prevent people from accessing your laptop.

Encrypt your Hard Drive:
Setting a password on your laptop is not enough to prevent hackers or unauthorized people from accessing your files.
If you are overly concerned about the security of your confidential data, then one of the best practices is to encrypt your hard drive to prevent data breaches.
But at times, full disk encryption is not always considered the best option for device protection.
Then you need to look for another option...
Cloud Storage vs Local Storage for Digital Evidence:
For long-term storage of digital evidence, which one is better cloud storage or local storage platforms?
You need to have trained IT employees to store each evidence file locally and create backups.
Moreover, local physical servers are more prone to external damage and hard to afford. Along with that, local servers have limited storage space. It is expensive to create and maintain the local storage system.
Cloud storage is most secure and scalable with additional layers of security that safeguard your digital evidence files.
According to the Salesforce Survey:
“94% of organizations claimed an improvement in security after switching to the cloud.”
Therefore, for protecting digital evidence you should opt for a cloud-based storage platform.
Read more about the differences between cloud vs on-premise storage.
VIDIZMO: Complete Solution for Protecting Digital Evidence:
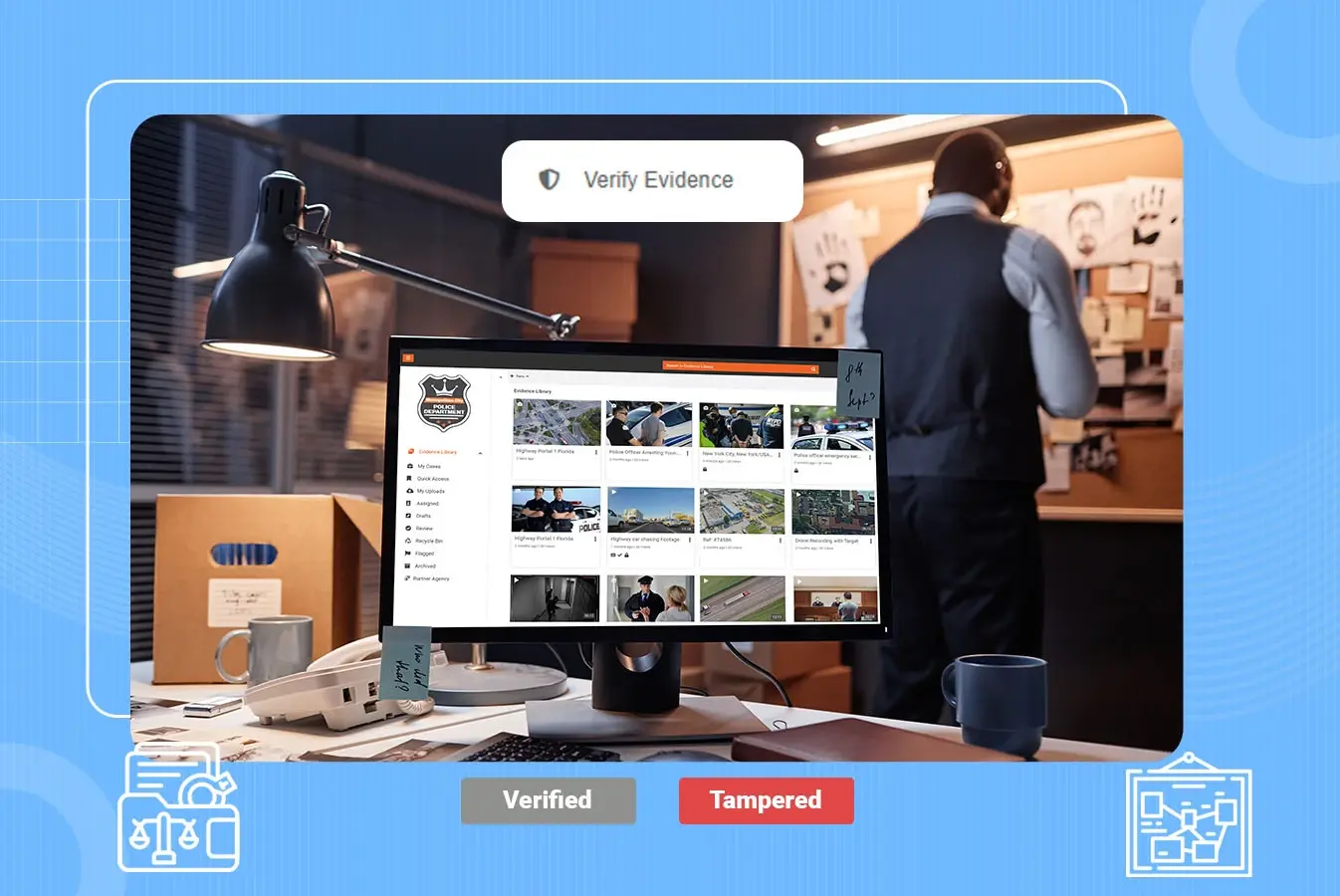
VIDIZMO provides an IDC-recognized Digital Evidence Management System, which is secure and easy-to-use software. It enables law enforcement agencies and other organizations to collect, store, handle and share ever-increasing digital evidence securely.
VIDIZMO DEMS is trusted for its secure storage, flexible deployment options, AI-powered features, and whatnot. The following are some of its remarkable features:
-
Collecting digital evidence from various sources such as dashcams, body-worn cameras, CCTV, drones, etc.
-
Securing and protecting digital evidence with FIPS-compliant end-to-end encryption.
-
A wide range of Deployment options includes Azure Cloud, AWS Cloud, Any Other Commercial or Government Cloud, on-premises data centers and hybrid infrastructure.
-
Detecting any type of tampering with the digital evidence since upload, through the help of SHA cryptographic hash values.
-
Sharing digital evidence securely on the same network with other officers, defense attorneys with a number of views, block download options, expiration dates etc.
-
Integrating with your existing IT applications such as computer-aided dispatch (CAD), record management system (RMS) and case management system (CMS).
-
Integrating with various SSO identity providers including Azure AD, OneLogin, Okta etc.
-
Maintaining a complete chain of custody reports in detail for tracking digital evidence across the portal.
-
Meeting compliance requirements such as CJIS, FedRAMP, GDPR etc.
-
Detecting, tracking, and redacting personally identifiable information appearing in videos.
-
Restricting specific regional IP for sharing digital evidence files.
-
Assigning specific roles to each user Role-Based Access control with certain permissions to access the portal.
-
Flagging of evidence to provide notifications and updates regarding any type of activity performed on the evidence to authorized people.
-
Sharing digital evidence with external users via a link with expiration dates. Creating multiple links for each evidence file.
For more details about VIDIZMO DEMS:
Jump to
You May Also Like
These Related Stories
Prevent Mishandling of Evidence with Digital Evidence Management
Prevent Evidence Spoliation With A Digital Evidence Management System




No Comments Yet
Let us know what you think